Contractors invest thousands of dollars in liability insurance protecting their company’s employees, heavy equipment, offices, and materials. But what about their data? Financial information, passwords, confidential information in contracts, and designs and blueprints are invaluable to businesses. With ransomware attacks happening in the United States every 11 seconds, it is essential for the construction industry to safeguard company data and networks.
So how is your cyber hygiene? With hybrid workspaces (yes, even in construction) becoming the new norm, data is no longer sitting in an office or on site – it’s mobile. We’ll walk you through what cybercriminals look for, how they target your business, and how to protect your vital information with cloud-based software.
What Cybercriminals Look For
Cybercriminals rely on human error to target businesses. They’re looking for sensitive company information and personal data to generate profit. The following are areas of your construction business they will typically seek out:
– Employee information, including social security numbers and bank details
– Material pricing
– Company financials like profit and loss
– Designs or blueprints
– Sensitive or confidential information in contracts
– Trade secrets
Bid Faster. Win More. Build Smarter.
Get your FREE account today to:
- Increase Team Efficiency
- Complete Estimates Faster
- Generate More Revenue

How Cybercriminals Target Your Business
Malware and Ransomware
Malware stands for “malicious software,” and it is intended to steal data and destroy computer systems. Ransomware is a type of malware, but cyber attackers encrypt your company’s data and demand paid ransom to unlock it.
Phishing
This type of cybersecurity threat is when attackers solicit people by email to obtain personal information, posing as a trustworthy organization. What may look like a reputable source at first glance will actually be a different source email or corporate name. They will even pose as company employees or executives.
Weak Passwords
With so many passwords needed in our digital world it is difficult to remember each one. Many people go the easy route and use passwords based on personal information – birthdays, address numbers, family names – or worse, use the same password for everything. This makes it an easy guessing game for attackers, and quite often they use those repeated passwords for a larger attack.
Apps and Connected Cloud Services
With the rise of cloud infrastructure services comes the rise of cybersecurity threats. Old software and outdated versions of apps are an easy target for cyberattacks. There is more room for vulnerabilities and possible insider threats.
Social Targeting
People feel safe to share vast amounts of personal information on social media as it’s used mostly for family and friends. Cybercriminals use fake accounts, developing “personalities” to groom people into clicking malicious links or giving away personal data.
Protecting Your Business From a Data Breach
Change your way of thinking about data security by being cybersmart. Instead of relying on a dedicated team – like your IT department – make everyone at the company responsible for securing important information.
– Use a cloud-based tool that protects your data in one place and has systems in place for your company’s data security, privacy, and user accessibility.
– Educate your employees about cybersecurity using training and tests with awareness programs like Ninjio or Proofpoint.
– Enforce strong password management and consider password managers like LastPass.
– Verify all domains and think before you click to avoid phishing.
– Be suspicious of activity asking for passwords or financial information.
– Enable remote updating and keep software updated on all devices.
– If employees use their own devices, make sure your company secures them.
– Consider using a virtual private network (VPN) like Bitdefender or Norton, and a personal/mobile hotspot with password protection.
Why Cloud-Based Tools Are Essential For Your Cybersecurity
Using a cloud-based software like STACK will make sure your data is protected by an iron-clad system. We are paying attention to your data security and valuing it before the fact, preventing data breaches and cyber-attacks on your company.
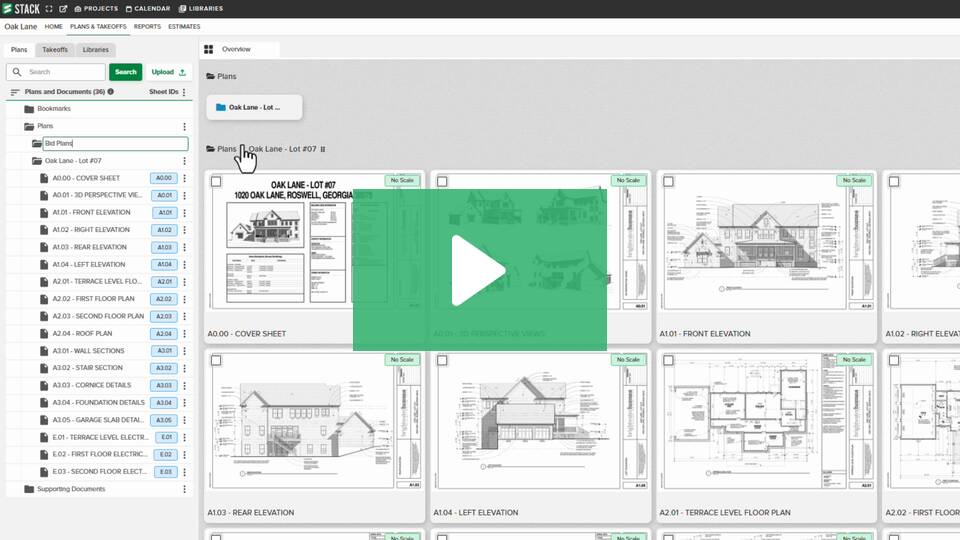
1. Common Data Environment
Cloud-based tools allow contractors to consolidate their data into one single source for more efficiency, productivity, and security. Company information spread across multiple locations, apps, or job sites only creates more vulnerabilities and exposure to attacks. For example, if you perform takeoffs in one system and estimating in another, essential project details and information must be moved or replicated in multiple places, posing a greater risk.
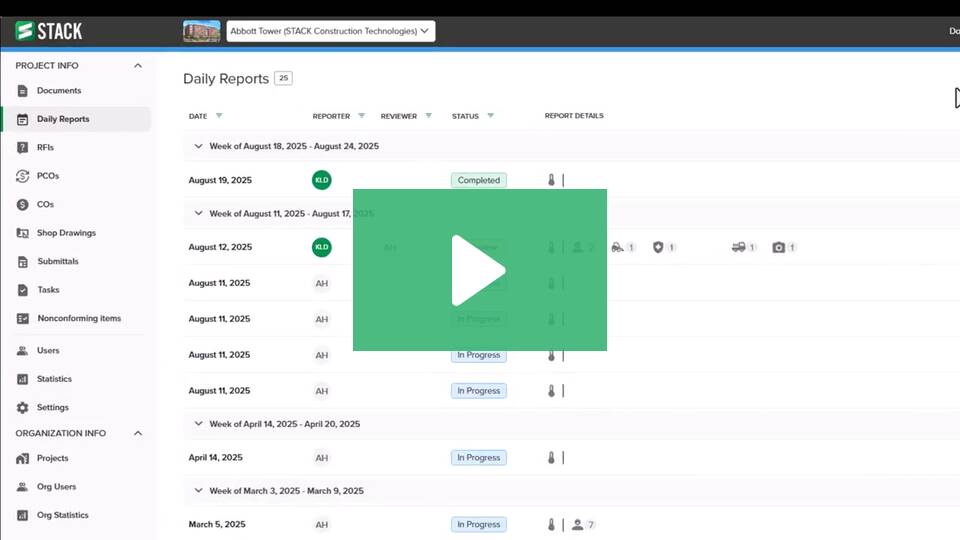
2. Administrative Ownership
Who has access to your data? Look for a construction software that offers user settings to ensure only authorized people have access to specific information. For example, you will want a trustworthy account owner as well as a backup person if someone is unavailable. Estimators should only have estimating abilities and clients should only have viewer settings. Protect yourself internally as well as externally.
3. Backups
Critical data should be backed up continuously. Data storage systems should be airtight and have plans in place to protect from any data loss.
4. Strong Password Requirements
Passwords are the digital keys to your data. Make them unique and make them long. Long passwords matter more than complexity when it comes to security.
5. Mobility
Cloud-based software ensures you have access to your data anywhere, anytime, but also provides automatic updates on features. SaaS solutions like STACK allow customers to implement the solution quickly and reduce the operational cost of maintaining your own software and hardware.
STACK Pro Tip
Add IT to your billable overhead or non-measured costs when sending estimates to clients. IT is no longer a trivial item; it is crucial to running a business. That includes software licenses, infrastructure, and tech personnel.