Cyber perpetrators know that the construction industry is behind in data security and privacy initiatives. Data breaches happen due to weaknesses in technology and user behavior, and these cyber criminals will research your company and employees to find access to your sensitive information.
Customers and GCs are becoming more concerned with how a company treats data, according to Construction Dive’s top cybersecurity trends of 2023. How is your company prepared to protect your data? We’ll guide you through how breaches happen and types of cyber-attacks, what data is compromised, why contractors should care, and how to be proactive and mitigate risk with cloud-based tools.
How a Security Breach Happens
Would you leave your keys in the ignition when parked on a busy city street? Didn’t think so. If your company’s information is vulnerable, you welcome the grand theft auto of data. Cybercriminals will target your company through:
– Weak passwords
– Outdated software
– Email scams
– No privileged account access for company data
– Unlocked devices or external hard drives

Four Types of Cybersecurity Attacks
A cybersecurity attack is when someone with harmful intent unlawfully accesses data, damages information, or disrupts digital operations. The following are four types of cybersecurity attacks to be mindful of:
1. Unauthorized Disclosure – When data is exposed to unauthorized parties. This can be as simple as leaving a confidential document on a photocopier or allowing coworkers to use your device.
2. Malicious Data Breach – When malicious insiders or external attackers gain unauthorized access to confidential data. A disgruntled employee can wreak havoc with sensitive company information.
3. Malware or Ransomware – Malware stands for “malicious software,” and it is intended to steal data and destroy computer systems. Ransomware is when cyber attackers encrypt your company’s data and demand a paid ransom to unlock it.
4. Phishing – When attackers solicit people by email to obtain personal information, posing as a trustworthy organization. What may look like a reputable source at first glance will be a different source email or corporate name. They will often pose as company employees or executives.
What Data is Compromised?
Cybercriminals are going for the jugular. They want employee personal information, financial data, sensitive designs, and your customer’s information. They target data like:
- Names
- Addresses
- Banking and payment information
- Company profit and loss reports
- Social Security numbers and Employee Identification Numbers
- Login criteria and passwords
- Project documents like estimates, budgets, and plans

Why Contractors Should Care About a Data Breach
A data breach is akin to getting your company’s identity stolen. It’s a long, drawn-out headache of cleaning up the flaws in your system’s infrastructure which takes a lot of time and money. The most daunting thing about a data breach is reputation damage. How you manage and mitigate cyber risk is directly linked to your company’s reputation.
There is a loss of trust when your employees and customers don’t feel safe if your company can’t protect sensitive data.
A GC’s sensitive designs and project data could be compromised, or a customer’s banking information could be stolen. In 2020, Canadian company Bird Construction experienced a data breach where secure government files were possibly accessed from their military and federal contracts.
Then comes the possibility of litigation. You can be held accountable for causing harm to other businesses or persons during a data breach from your negligence to secure your data and systems. Besides the possibility of a lawsuit, you can face regulatory fines for violating state privacy laws.
After a data breach, you’ll likely face a company network shutdown causing scheduling delays and unhappy customers or GCs. This is when the cyber cleanup occurs – changing account numbers, updating login and passwords, and executing company-wide cybersecurity protection plans.
Be Proactive About Cybersecurity
It’s time to get cybersmart. You can no longer solely rely on your IT department. Everyone at your company should be responsible for securing important information. Everyone at your company should be responsible for securing important information.
– Use a cloud-based solution that protects your data in one place and has systems for data security, privacy, and user accessibility.
– Maintain oversight of your partners and vendors. Be aware of their cyber wellness.
– Add Data Security into your contracts. A data security incident at a General Contractor or supplier may have serious consequences when it exposes your business’s information. You may want to consider including legal language in the event the vendor or GC suffers a data breach.
– Educate your employees about cybersecurity using training and tests with awareness programs like Ninjio or Proofpoint.
– Enforce strong password management and consider password managers like LastPass.
– Enable remote updating and keep software updated on all devices.
– If employees use their own devices, make sure your company secures them. -Consider using a virtual private network (VPN) like Bitdefender or Norton, and a personal/mobile hotspot with password protection.
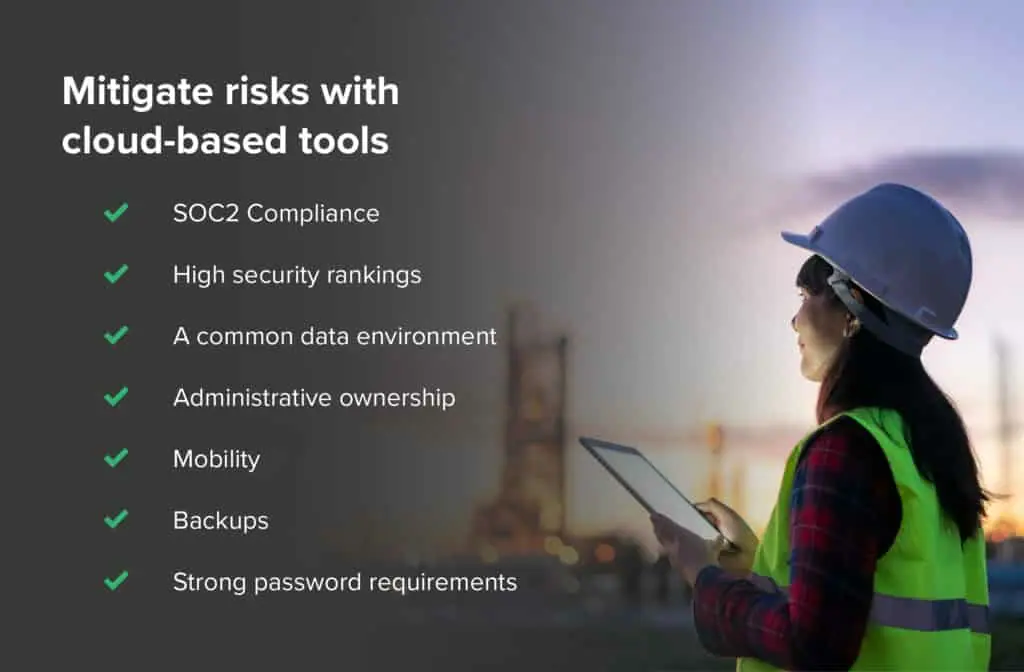
Mitigate Risk with Cloud-Based Tools
Using a cloud-based platform like STACK will make sure your data is protected by an iron-clad system. We are paying attention to your data security and valuing it before the fact, preventing data breaches and cyber-attacks on your company. Look for solutions that provide:
1. SOC2 Compliance
Find solutions that are SOC 2 compliant, which requires companies to manage customer data based on security, availability, processing integrity, confidentiality, and privacy. STACK is SOC 2 compliant and has transparent policies on how we maintain our systems. No need to do any additional vetting, we already went through the rigorous processes to protect your data! Bonus: STACK is also PCI DSS compliant – a security standard for the card payment industry.
2. High Security Rankings
STACK ranks 98/100 on SecurityScorecard, the global leader in cybersecurity ratings and the only service with millions of organizations continuously rated. With our “A” rating, STACK is 7.7 times LESS likely to be impacted by a cybersecurity breach.
3. A Common Data Environment
Cloud-based tools allow contractors to consolidate their data into one single source. Sensitive company information spread across multiple locations, apps, or jobsites only creates more vulnerabilities and exposure to attacks.
4. Administrative Ownership
Who has access to your data? Use the “zero trust” principle and look for construction software that offers user settings to ensure that only authorized people have access to specific information. For example, Estimators should only have estimating abilities and clients should only have viewer settings. Protect yourself internally as well as externally.
5. Mobility
Cloud-based software ensures you have access to your data anywhere, anytime, but also provides automatic updates on features.
6. Backups
Critical data should be backed up continuously. Data storage systems should be airtight and have plans in place to protect from any data loss.
7. Strong Password Requirements
Passwords are the digital keys to your data. Make them unique and make them long. Long passwords matter more than complexity when it comes to security.
STACK Pro Tip!
Add IT to your billable overhead or non-measured costs when sending estimates to clients. IT is no longer a trivial item; it is crucial to running a business. That includes software licenses, infrastructure, and tech personnel.
Cybersmart with STACK!
STACK is committed to delivering a system with industry-leading security, availability, and reliability. Our infrastructure and operational best practices safeguard your data.